Trustless Proof of Reserves: Why Crypto Institutions Need More Than a Snapshot

In crypto, the word "trust" has always been paradoxical. The entire industry was built on the premise that you shouldn't need to trust anyone, that code and cryptography could replace handshakes and promises. And yet, when it comes to proving that institutions actually hold what they claim to hold, the industry has relied on exactly the kind of trust-based mechanisms it was designed to eliminate.
The collapse of FTX, Celsius, and Voyager didn't just destroy billions in value. It also exposed a fundamental gap: there was no reliable, tamperproof way to verify that custodial platforms and institutional players had the reserves they claimed. The response, Proof of Reserves (PoR) – which allows an exchange to publicly verify that it holds the user funds it claims to – was a step in the right direction. But most implementations today still fall short of the trustless standard that crypto demands.
This article explores what trustless Proof of Reserves actually means, why current approaches leave dangerous gaps, and how a new architecture built on decentralized data warehouses and zero-knowledge proofs is finally closing them.
The Problem With Traditional Proof of Reserves
The concept of Proof of Reserves is simple: an entity demonstrates that it holds enough assets to cover its obligations. In practice, most PoR implementations follow a familiar pattern: an exchange takes a snapshot of its wallet balances, organizes user liabilities into a Merkle tree, and publishes a report (sometimes verified by a third-party auditor) showing that assets meet or exceed liabilities.
This approach has three structural weaknesses that undermine its value.
Snapshots are stale the moment they're taken. A PoR report tells you what an entity held at only one specific point in time. Between snapshots, funds can be moved, lent out, or pledged as collateral elsewhere. Monthly or quarterly attestations create windows, measured in weeks (or as long as three months), in which anything can happen. Historically, things have happened.
The auditor becomes the trust bottleneck. When a third party verifies reserves, users are trusting that the auditor is competent, independent, and not subject to pressure. After FTX's collapse, questions arose about the reliability of some auditing firms in the crypto space. Simply replacing one trust assumption (the exchange) with another (the auditor) doesn't solve the fundamental problem.
Liabilities are often invisible. Most PoR reports prove assets exist but say nothing about debts. An exchange could hold $1 billion in crypto while carrying $3 billion in offchain liabilities, and the PoR report would still appear perfectly healthy. Without a complete picture of both sides of the balance sheet, reserve claims are fundamentally incomplete.
For institutional players like market makers, trading firms, and asset managers who hold funds across multiple exchanges, these gaps are even more pronounced. Their reserves aren't sitting in one place; they're spread across dozens of accounts on different platforms, denominated in different assets, and constantly moving. A single snapshot from a single exchange tells a lender almost nothing about the firm's true financial position.
What "Trustless" Actually Means
The word "trustless" gets thrown around a lot in crypto, but in the context of proof of reserves, it has a specific and important meaning: that no single party can manipulate the data or the verification process. Not the entity being audited, nor an auditor, nor a database administrator.
Achieving this requires solving three distinct problems simultaneously.
First, the data itself must be collected without any party being able to alter it. If an exchange self-reports its balances, or if a single intermediary fetches and relays the data, that inherently breaches the trustless model by opening up the potential for manipulation. Trustless ingestion means the data is fetched and attested through hardware-secured environments in which even the operator can't see or modify what's being collected.
Second, the data must be stored in a way that's immutable and independently verifiable. A centralized database, no matter how well-secured, has an administrator who can change records. Decentralized storage eliminates that single point of control, making historical reserve data a permanent, tamperproof record.
Third, the computations run against that data must themselves be provably correct. The queries, aggregations, and KPIs that lenders and counterparties actually care about need to carry their own proof of correctness. It's not enough to store honest data if the reports drawn from it can be manipulated. This is where zero-knowledge proofs become essential.
The Architecture of Trustless PoR
Building a system that meets all three requirements demands a fundamentally different architecture from that of traditional PoR. Rather than periodic snapshots verified by trusted parties, a trustless approach creates a continuous pipeline from raw exchange data to verifiable, queryable reserves.
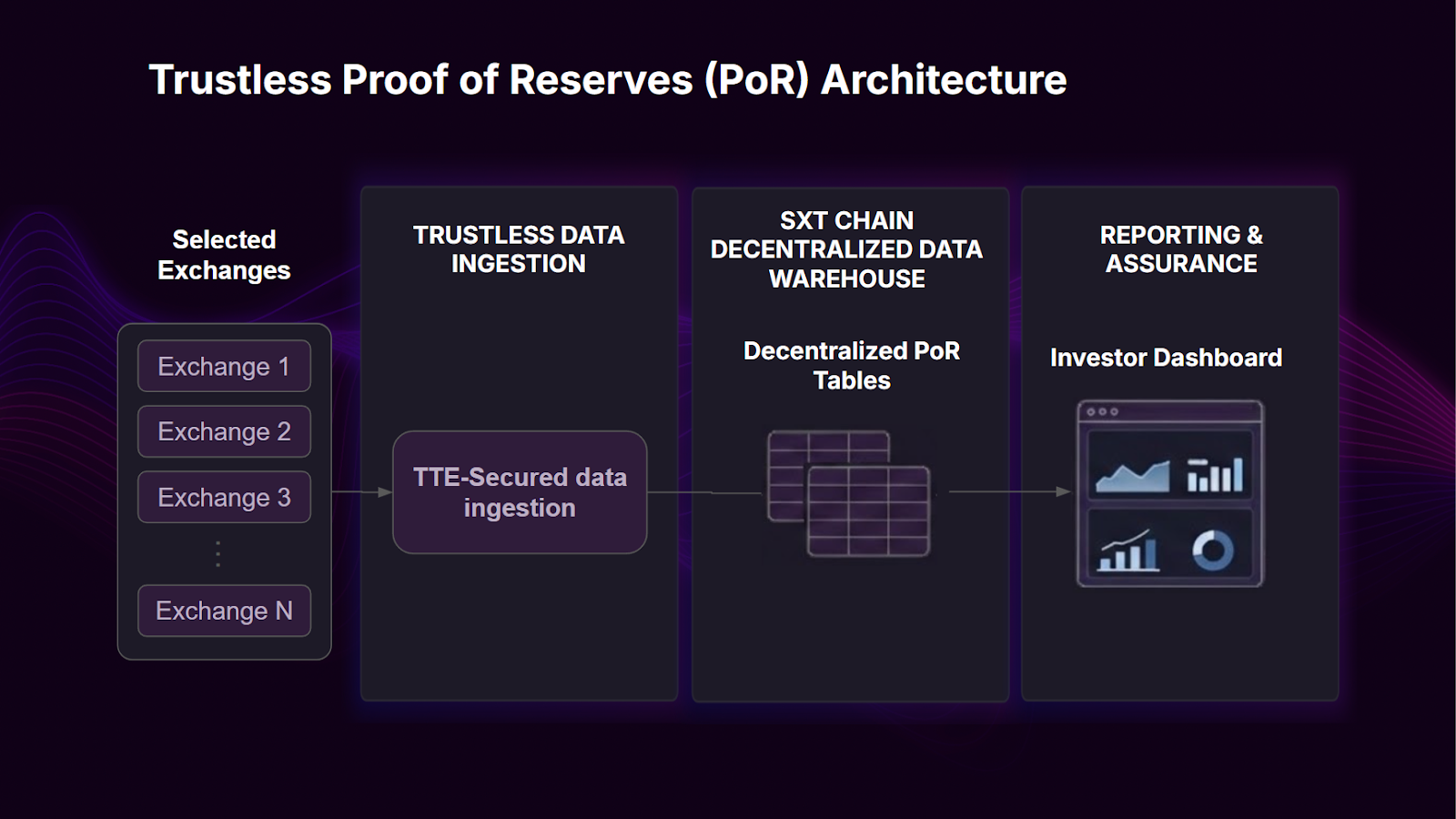
Trustless Data Ingestion
The first link in the chain is transporting balance data from exchanges without introducing trust assumptions. This is accomplished through Trusted Execution Environments (TEEs), hardware-isolated enclaves where code runs in a way that even the machine's operator can't observe or tamper with.
In practice, a TEE-based system polls exchange REST APIs on a regular schedule, fetching balance data using encrypted credentials that never leave the secure enclave. The output includes both the balance data itself and a hardware-signed attestation: a cryptographic proof that the data was fetched directly from the source and delivered unmodified.
This provides a critical distinction from traditional approaches: there's no human in the loop, no intermediary with access to modify the numbers. The attestation is generated by the hardware itself, creating a verifiable chain of custody from the exchange API to the downstream storage layer.
Decentralized Data Storage
Once attested, the balance data is indexed into a decentralized data warehouse. This is where SXT Chain adds a critical layer. SXT Chain indexes attested data into decentralized SQL tables that are structured, queryable, and anchored to cryptographic commitments. The data warehouse isn't a centralized copy sitting on someone's server. It's a network of validators maintaining a replicated, tamper-evident dataset where every table's structure and content is cryptographically committed.
The result is an immutable data layer in which reserve history is stored in a format that's both verifiable and practical. Lenders, auditors, or anyone with permission can run SQL queries against months or years of reserve data, and the underlying data can't be changed after the fact because it's anchored to onchain events and cryptographic commitments.
Verifiable Computation with Proof of SQL
Storage and ingestion are necessary but not sufficient. The real power of a trustless PoR system comes from what happens when you query the data.
Proof of SQL is a zero-knowledge proof protocol purpose-built for database queries. When a user runs a SQL query against reserve data (aggregating total balances across exchanges, computing a coverage ratio over time, and so on), the system doesn't just return the result; it also generates a succinct cryptographic proof demonstrating that the query was executed faithfully against the committed, untampered dataset.
A lender reviewing a borrower's reserve position doesn't need to trust the dashboard, the hosting provider, or the data warehouse operator. They can mathematically verify that the number they're looking at is correct.
For institutional use cases, this changes the dynamics fundamentally. Instead of trusting a PDF report or a third-party attestation, counterparties get a mathematically guaranteed answer to the key question: "Does this entity hold what they claim to hold?"
Why This Matters for Institutional Crypto
The greatest beneficiaries of trustless PoR are institutional players operating across multiple exchanges: market makers, proprietary trading firms, and digital asset managers. These entities face a specific problem: they hold significant reserves spread across many platforms, but they can't efficiently prove this to counterparties.
The economic consequences are real. When lenders can't verify a borrower's reserves with confidence, they price in uncertainty. That means higher interest rates, lower credit limits, and more restrictive lending terms. The opacity isn't just an inconvenience; it's a direct cost on the balance sheet.
A trustless PoR system converts that opacity into a competitive advantage. When a firm can point to a continuously updated, cryptographically verified record of its reserves across every exchange on which it operates, lenders have the confidence to offer better terms. Transparency, backed by mathematical proof rather than promises, reduces the risk premium.
The same architecture also serves regulatory compliance, investor reporting, and counterparty due diligence. Any context in which an institution needs to demonstrate its financial position benefits from data that is provably accurate and historically immutable.
The Privacy Question
One reasonable objection to a fully transparent reserve system is that some institutions may not want their exact balances publicly visible. A market maker's positions across exchanges can reveal trading strategies, and public balance data could be exploited by competitors.
This is a solvable problem, and it doesn't require sacrificing verifiability. Encryption can be applied at the ingestion layer to individual balance data points before they're written onchain. Authorized counterparties (lenders, regulators, or specific investors) could then access a private view in which encrypted data is decrypted at the edge, visible only to those with permission.
The key point is that privacy is additive, rather than a trade-off. The underlying data remains onchain and verifiable. Authorized parties who can access the data and run queries against it receive results backed by Proof of SQL, confirming that the computation was executed faithfully against untampered data. Competitors without access see nothing useful, while lenders with permission get cryptographically verified answers.
From Point-in-Time to Continuous Assurance
Perhaps the most important shift that trustless PoR enables is moving from periodic attestation to continuous assurance. Traditional PoR is an event, a snapshot taken monthly or quarterly, sometimes less often. Between snapshots, anything can happen.
With a decentralized pipeline that polls exchange APIs daily (or more frequently) writes attested data to the chain and makes that data queryable with provable correctness, reserve verification becomes an ongoing state rather than a periodic event. A lender doesn't need to wait for the next audit cycle to know where things stand. They can simply query the latest attested data at any time and receive a verifiable answer.
This continuity doesn't just improve transparency; it changes the nature of the trust relationship between institutions and their counterparties. Instead of "trust us between audits," the message becomes "verify our reserves at any time."
How Space and Time Makes This Real
Implementing a trustless PoR pipeline is not trivial, but it no longer requires building from scratch. Space and Time has assembled the full stack into a working solution.
The pipeline starts with TEE-secured data ingestion that polls exchange APIs and produces hardware-signed attestations. Attested balance data is indexed into SXT Chain's decentralized database, in the form of immutable, queryable SQL tables. A dashboard layer on top queries the warehouse in real time, with Proof of SQL ensuring that every result is cryptographically verified.
The architecture is modular by design: new exchange integrations plug into the existing pipeline, extending the unified reserve view without requiring new infrastructure. Whether a firm holds funds on three exchanges or fourteen, the system easily scales to cover the full footprint.
What remains is adoption: institutions recognizing that verifiable transparency isn't just a compliance exercise, but also a financial advantage.
The Bottom Line
Proof of Reserves was always a good idea. The problem was execution: snapshots, trusted auditors, and incomplete liability coverage left gaps that eroded the very trust PoR was supposed to build.
Trustless Proof of Reserves closes those gaps by removing trust assumptions from every stage of the pipeline, from data collection to storage to computation and reporting. Cryptographic attestation replaces self-reporting. Decentralized, immutable storage replaces centralized databases. Zero-knowledge proofs replace trust in the report generator.
For Web3 institutions, this isn't a theoretical improvement; it's a practical path to better lending terms, stronger counterparty relationships, and a provable track record of financial integrity. In an industry that was built on the promise of trustlessness, it's time that Proof of Reserves actually lived up to – and contributed to – that standard.
Make your reserves continuously verifiable with trustless Proof of Reserves here

